AWS Identity Access Management – IAM
AWS IAM Overview
·
AWS Identity and
Access Management (IAM) is a web service that helps you securely control access
to AWS resources for your users.
·
IAM is used to
control
· Identity – who can use your AWS resources (authentication)
· Access – what resources they can use and in what ways (authorization)
·
IAM can also keep
your account credentials private.
·
With IAM, multiple
IAM users can be created under the umbrella of the AWS account or
temporary access can be enabled through identity federation with corporate
directory.or third party providers
· IAM also enables access to resources across AWS accounts.
Best AWS Training Institute in Noida...
IAM Features
1.
Shared access to
your AWS account
2.
Grant other people
permission to administer and use resources in your AWS account without having
to share your password or access key.
3.
Granular permissions
4.
Each user can be
granted with different set granular permissions as required to perform their
job
5.
Secure access to AWS
resources for applications that run on EC2
6.
IAM can help provide
applications running on EC2 instance temporary credentials that they need in
order to access other AWS resources
7.
Identity federation
8. IAM allows users to access AWS resources, without requiring the user to have accounts with AWS, by providing temporary credentials for e.g. through corporate network or Google or Amazon authentication
9.
Identity information
for assurance
10.
CloudTrail can be
used to receive log records that include information about those who made
requests for resources in the account.
11.
PCI DSS Compliance
12.
IAM supports the
processing, storage, and transmission of credit card data by a merchant or
service provider, and has been validated as being Payment Card Industry Data
Security Standard (PCI DSS) compliant
13.
Integrated with many
AWS services
14.
IAM integrates with
almost all the AWS services
15.
Eventually
Consistent
16.
IAM, like many other
AWS services, is eventually consistent and achieves high availability by
replicating data across multiple servers within Amazon’s data centers around
the world.
17.
Changes made to IAM
would be eventually consistent and hence would take some time to reflect
18.
Free to use
19.
IAM is offered at no
additional charge and charges are applied only for use of other AWS products by
your IAM users.
20.
AWS Security Token
Service
21.
IAM provide STS
which is an included feature of the AWS account offered at no additional
charge.
22.
AWS charges only for
the use of other AWS services accessed by the AWS STS temporary security
credentials.
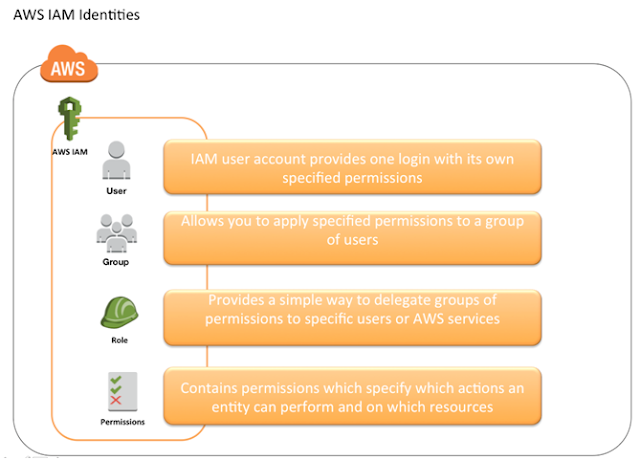
Identities
IAM identities determine who can access and help to provide
authentication for people and processesin your AWS account
Account Root User
§
Root Account
Credentials are the email address and password with which you sign-in into the
AWS account
§
Root Credentials has
full unrestricted access to AWS account including the account security
credentials which include sensitive information
§ IAM Best Practice – Do not use or share the Root account once the AWS account is created, instead create a separate user with admin privilege
§
An Administrator
account can be created for all the activities which too has full access to the
AWS account except the accounts security credentials, billing information and
ability to change password
IAM Users
·
IAM user represents
the person or service who uses the access to interact with AWS.
· IAM Best Practice – Create Individual Users
·
User credentials can
consist of the following
· Password to access AWS services through AWS Management Console
· Access Key/Secret Access Key to access AWS services through API, CLI or SDK
·
IAM user starts with
no permissions and is not authorized to perform any AWS actions on any AWS
resources and should be granted permissions as per the job function requirement
· IAM Best Practice – Grant least Privilege
·
Each IAM user is
associated with one and only one AWS account.
·
IAM User cannot be
renamed from AWS management console and has to be done from CLI or SDK tools.
·
IAM handles the renaming
of user w.r.t unique id, groups, policies where the user was mentioned as a
principal. However, you need to handle the renaming in the policies where the
user was mentioned as a resource
IAM Groups
·
IAM group is a
collection of IAM users
·
IAM groups can be
used to specify permissions for a collection of users sharing the same job
function making it easier to manage
· IAM Best Practice – Use groups to assign permissions to IAM Users
·
A group is not truly
an identity because it cannot be identified as a Principal in an access policy.
It is only a way to attach policies to multiple users at one time
·
A group can have
multiple users, while a user can belong to multiple groups (10 max)
·
Groups cannot be
nested and can only have users within it
·
AWS does not provide
any default group to hold all users in it and if one is required it should be
created with all users assigned to it.
·
Renaming of a group
name or path, IAM handles the renaming w.r.t to policies attached to the
group, unique ids, users within the group. However, IAM does not update the
policies where the group is mentioned as a resource and must be handled
manually
·
Deletion of the
groups requires you to detach users and managed policies and delete any inline
policies before deleting the group. With AWS management console, the deletion
and detachment is taken care of.
Comments
Post a Comment